Module 3: Planning Administrative Access | Windows Security Fundamentals
Planning Administrative Access involves designing secure methods to assign administrative privileges by using role-based models, group strategies, and the principle of least privilege, ensuring only authorized personnel can perform critical system tasks.
Determining the Appropriate Administrative Model for Secure and Efficient IT Management
Determining the Appropriate Administrative Model involves choosing the right approach—centralized, decentralized, or hybrid—for assigning administrative roles and permissions, ensuring secure, scalable, and efficient management of IT resources.
- Choosing Centralized Administrative Models
- Choosing Decentralized and Hybrid Administrative Models
- Decentralized Administration
- Hybrid Administration
- Identifying Network Resource Administrative Tasks
- Identifying Administrative Tasks
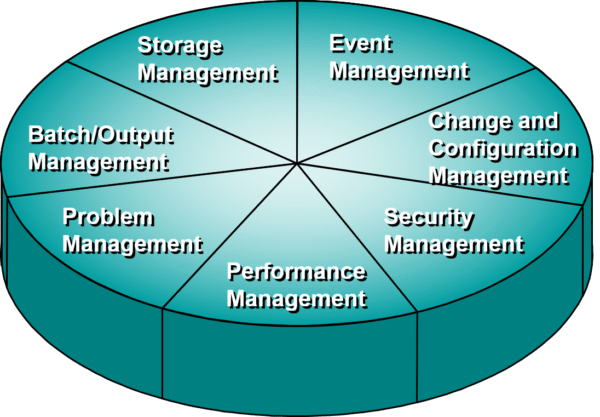
- Defining Security Management Tasks
- Secure Physical Systems and Devices
- Manage Users, Groups, and Policies
- Define and Implement Authentication and Data Transmission Security
- Control and Monitor Access to Shared Resources
- Create and Implement an Audit Policy
- Create and Implement a Backup and Recovery Plan
- Create and Implement Desktop Policies
Designing Administrative Group Strategies for Efficient Access Control
Designing Administrative Group Strategies involves structuring role-based administrative groups to delegate tasks efficiently and securely, minimizing risks and ensuring proper access control across systems.
- Creating Custom Groups
- Nesting Groups
- Managing Administration Memberships
- Using Restricted Groups
- Monitoring Memberships
Planning Local Administrative Access for Individual System Security
Planning Local Administrative Access refers to assigning administrative rights on individual machines carefully to ensure only trusted users can perform sensitive actions, reducing the risk of unauthorized access or system compromise.
- Controlling Physical Administration Points
- Physical Security
- Smart Card Logon Access
- Planning Logical Security Settings
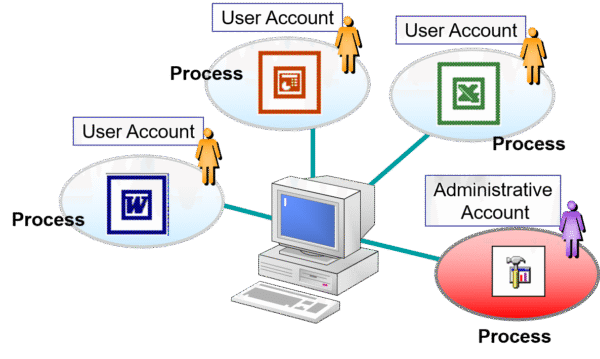
- Using the RunAs Service
- Running Applications
- Providing Alternate Credentials
Planning Remote Administrative Access for Secure System Control
Planning Remote Administrative Access involves setting up secure methods for administrators to manage systems remotely, using strong encryption, authentication protocols, and access control to prevent unauthorized entry and maintain system integrity.
- Encrypted Authentication and Data Transmission
- Customizing Microsoft Management Console
- Restricting Access to MMC
- Distributing MMC
- Using Terminal Services for Remote Administration
- User Rights
- Administrator Security
- Data Encryption
- Additional Security Considerations
- Using Telnet for Remote Administration

Add comment