Module 5: Securing Windows-Based Computers for Maximum Protection
Securing Windows-Based Computers involves applying security best practices such as configuring firewalls, enforcing updates, enabling antivirus, and managing user access to protect systems from malware, unauthorized access, and data breaches.
Designing Account Policies and Group Policy
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.
- Designing Account Policies
- Prioritizing Group Policy Application
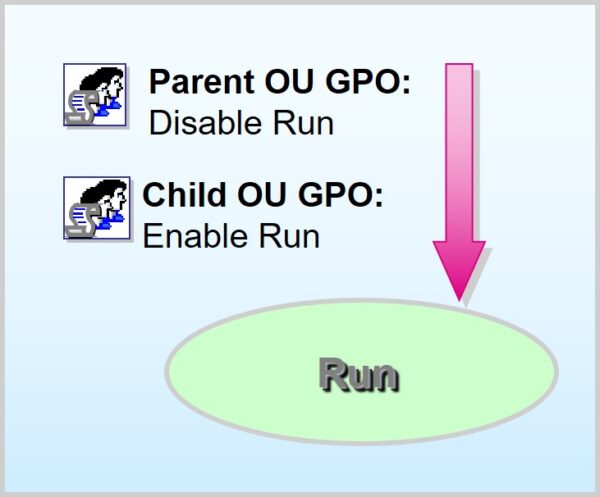
- Order of GPO Application:
- Local Computer Site Domain Parent OUs Child OUs
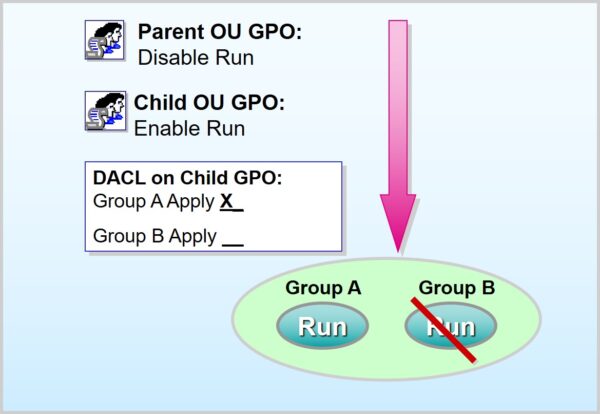
- Filtering Group Policy
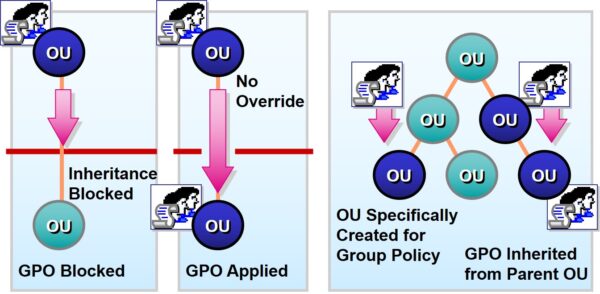
- Designing for Group Policy Inheritance
Planning Account Creation and Location for Secure Windows Environments
Planning Account Creation and Location involves designing a structured strategy for creating user accounts and determining where they reside—locally or in Active Directory—to support secure access, scalability, and centralized management in Windows environments.
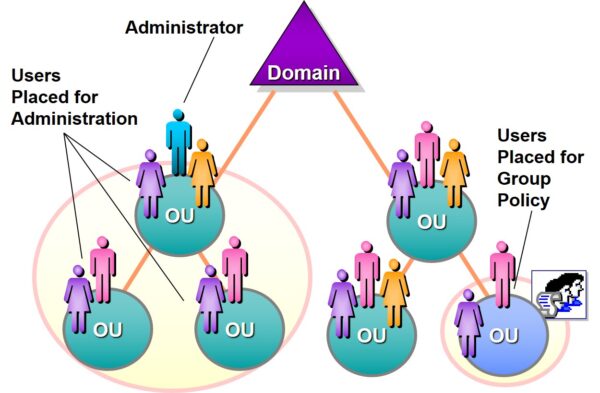
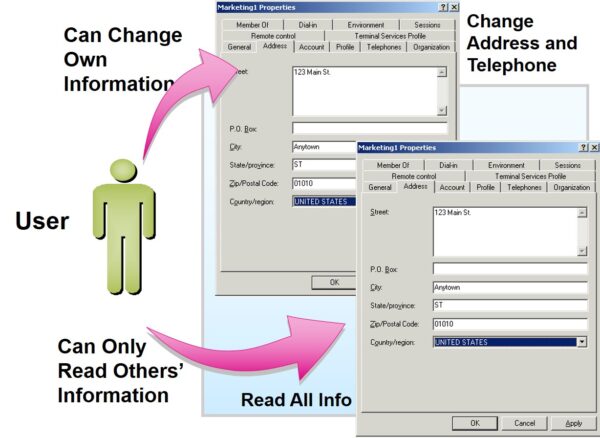
- Placing User Accounts
- User Account Default Settings
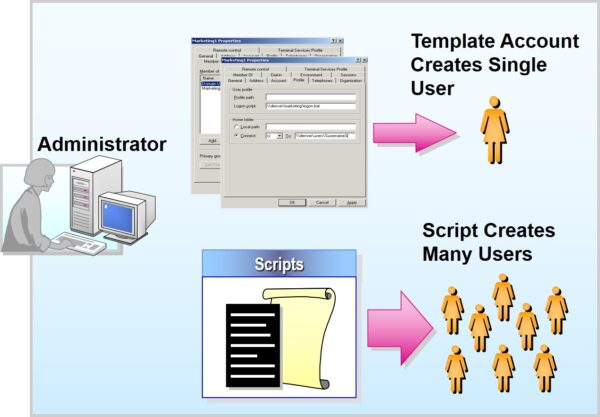
- Creating Accounts Using Templates and Scripts
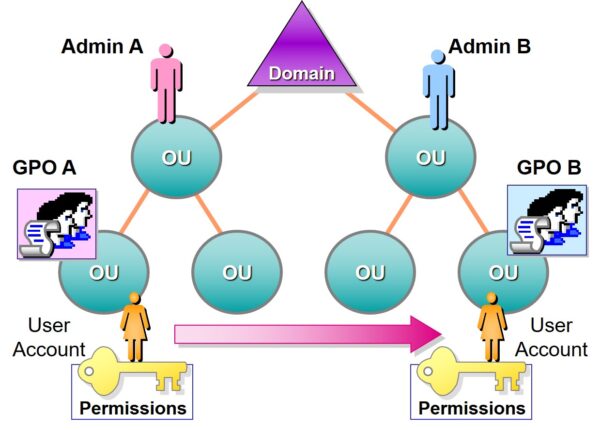
- Moving User Accounts Within Active Directory
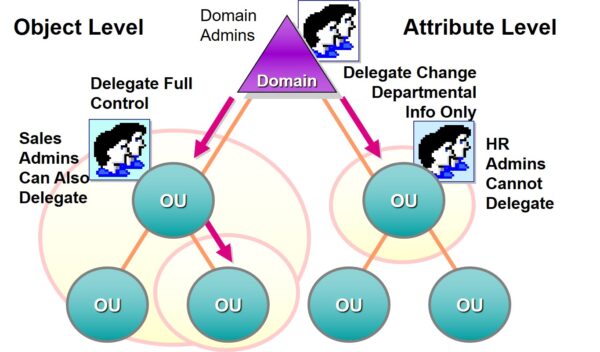
Planning Delegation of Authority | Designing Windows Security
Planning Delegation of Authority refers to defining which users or groups are granted specific administrative responsibilities within a Windows environment, ensuring secure and efficient task management through role-based access control and the principle of least privilege.
Auditing User Account Actions
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.
- Selecting Events to Audit
Event
Account logon
Account management
Directory service access
Logon
Object access
Policy change
Privilege use
Process tracking
System
Example
Domain controller receives a request to validate a user account
Administrator creates, changes, or deletes a user account or group
User gains access to an Active Directory object
User logs on or off a local computer
User gains access to a file, folder, or printer
Change is made to the user security options, user rights, or Audit policies
User exercises a right, such as taking ownership of a file
Application performs an action
User restarts or shuts down the computer
- Planning an Audit Strategy
- Auditing Success and Failure
- Success can document actual security breach
- Failure may indicate attempted security breach
- Deciding What to Audit
- Low security: minimal auditing
- High security: increased auditing
- Excessive Auditing
- Fills security log
- Difficult to interpret

Add comment